I heard it said once when I was young, a while ago, “If you control perception, you control events.” I didn’t make much sense of it then, but it really stayed with me.
As time has gone on and I delved farther and farther into the realms of security and personal protection, and all the knowledge, skills and wisdom passed down regarding them that simple aphorism took on new and clear meaning.
Perception, for most people, is reality: they will not stop to question the sum total of the information presented to them and gathered by their senses if they have no reason to. They will act and think about that total without a second thought, with varying consequences.
Control of perception makes classic magic, sleight-of-hand, possible. Controlling perception can make the visible invisible, the weak appear strong and the great seem meager.
Deception is the umbrella term for making someone believe something that is not true. Ignoring the strong social connotations of deception to assess it as a tool for protection and defense reveals it to be an ancient and powerful skill in defense and conflict.
Deception, skillfully employed, is in essence a cognitive weapon, one that functions by attacking the thought processes of your foes by shaping their perception: They see and believe only what you choose to show them.
One of the oldest and most ubiquitous forms of deception is the decoy, a person or thing designed to be a distraction that squanders the time, energy, and willpower of an enemy on a fruitless pursuit. Alternatively, it may lure them into a disadvantageous position, or get them to reveal their intentions if they are hidden.
Combined with other elements of defense and subterfuge, a decoy can create ample opportunity for a defender to escape or counterattack, or merely exhaust and frustrate an attacker as they blunder around attacking useless targets in a veritable hall of mirrors.
In this article, I’ll give all the good guys and good gals out there a thorough brief on decoys as a tool for self-defense and other elements of deception that can be layered on top of them as part of a comprehensive self-defense plan.
Examples of Decoy Usage
Decoys are used in all sorts of professions and ventures, from military operations to law enforcement and even civilian pastimes. No matter who is using them or why, the end goal of a decoy is always the same: sending your quarry else on a wild goose chase or enticing them to move out of position or reveal their intentions.

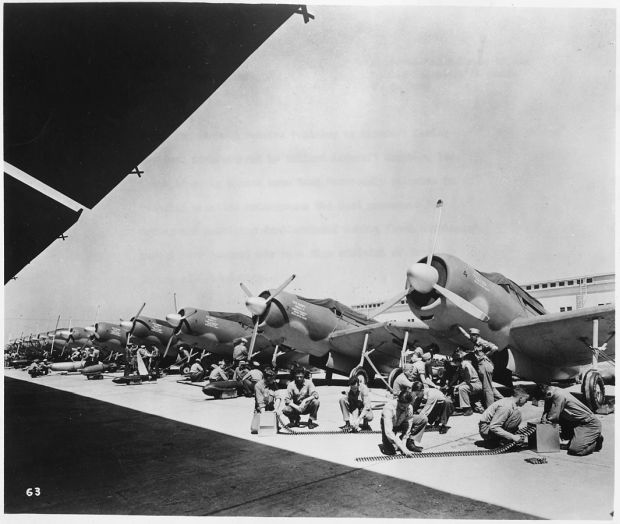
Some famous and well-known examples are the inflatable tanks and other vehicles used by the Allies to give German recon planes the bamboozle prior to the commencement of Operation Overlord in World War II.
Other military decoys are the helmet on a stick employed by hiding infantry to convince enemy snipers to reveal themselves. Police decoys in particular have a rich and storied history, from the bait cars used to nab lurking car thieves to the not-really-a-hooker undercover cops conducting prostitution stings.
Civilians are no slouches when it comes to decoy use, either. Hunters of all stripes use decoys to lure animals closer or move them out of certain areas. Gardeners and homeowners use decoys shaped like birds of prey to keep other birds and nibbling mammals out of flowerbeds and veggie patches.
The humble scarecrow is a folksy and traditional decoy used by farmers to keep crows and other nuisance birds at a distance (and is also a great example of decoy failure, many times! More on that later).
Even in daily life, decoy elements are used to attract and bind attention so people can accomplish a task. If you have ever used an accomplice to create a distraction or lure someone away so you could finalize plans for their surprise party, congratulations, that is Decoys 101.
Employing decoys for protection and self-defense is a thinking-persons game, and may require a little thought but lessons can be learned from each of these examples above. Before we get into the nuts and bolts of all of that, let’s break down what makes for an effective decoy and further how to employ them for maximal impact on our attackers.
Anatomy of a Decoy
A decoy may take any shape or form depending on what you are trying to accomplish. Decoys can be improvised by the user or bought purpose-made.
For our purposes, most of our decoys will be purpose-made, as you will need to assess your unique situation and objectives then construct your decoys accordingly in support of your goals.
The two most important elements of decoy creation are fidelity, or realism, and location, which are derived from placement in relation to your actual assets, line of approach by bad guys, and so forth. I cannot stress how important both of these are to the successful employment of your ruse.
While executing one element well may be enough to get you results, you will see far greater success and truly flummox your foes by going the extra mile on both.
A high-fidelity decoy appears to be the “real thing” to your adversary, under all but the closest scrutiny. A realistic decoy is important because it ensures your foe will key on it and accept it as the thing it appears to be instead of what it is; a fake or distractionary device.
A high-fidelity decoy will closely mimic an actual target in all its essential features: size, shape, color, texture, contents, weight, etc. depending on the nature of the intended target.
Smart locating of a decoy is similarly critical because it further convinces the instigator that they have the right target or the real thing. Plausibility, context, and believability are the watchwords when considering smart location.
Poorly chosen locations can ruin an otherwise masterfully crafted and high-fidelity decoy. What if in the WWII example above our German recon planes saw those inflatable tanks bobbing in the middle of a lake like rubber ducks? Exactly- no dice.
Consider the differing levels of effectiveness thanks to varying realism among decoys of the same type in the following examples. Also consider how differently they may be perceived if their location was altered.
- A decoy bait car used by police that appears to be a newer, nicer model left unattended in a bad part of town, versus a busted-up jalopy left in the same place. Which is more appealing to thieves? Is there a chance that a clever thief would be spooked by a too-nice car in their AO? Would that same nice car, left running and unlocked still be a target opportunity in a nicer part of town?
- A decoy safe or lockbox that is not weighted or full of convincing-sounding items versus one that is carefully secured, weighted, and full of jangly metal bits suggesting jewelry or precious metal? How would the decoy work if it were in view of a fullsize standing safe? Would it work better to “satiate” a burglar if the standing safe was hidden?
- For hunting waterfowl, decoys that are crudely shaped, painted, and scattered versus ones that are finely detailed, patterned, and arranged to closely mimic the appearance and habits of the birds you are after? Would an exquisitely crafted decoy placed haphazardly work well enough, fairly, or not at all? How about the reverse; would poorly made decoys placed with great care and attention work well?

Those are just a few examples to get your mind churning over the interplay of fidelity and location for determining the effectiveness of any decoys you use. In the next sections, we’ll be going over specific examples and techniques that are more germane to personal security and preparedness.
You Must Consider Your Adversary’s Position When Designing a Decoy
This roleplaying is an important part of effective decoy design and employment. What is your adversary looking for? What is he expecting to see? What does “success” look and feel like to him? You must be able to put yourself in their place and see the world as they see it to effectively deploy your decoy.
Take it down a few layers; assuming his quarry is at least tangentially aware of his presence, and were taking action to thwart him, what might they do, and how might he then defeat that?
While a good decoy well executed will spoof most people initially, dumb and smart alike, you should assume a worst-case scenario, one in that you’re dealing with a clever hunter who will not be taken so easily.
A decoy that is further hidden or defended as if it were the real thing will only set the hook deeper in the mind of your foe that he is on the right track.
Typically, discovering that you have been so thoroughly had after much hard work and strain is very demoralizing, and oftentimes someone who has been tricked so will not persist in their search for fear of exposing themselves and wasting even more energy and time
Decoy Usage as Part of Your Preparedness Plan
Decoys have a place in a security plan from large-scale operations down to the personal level. Decoys used in conjunction with other elements of security can help protect and preserve your supplies and other assets from those who would steal or despoil them, and have a place in your plans both pre- and post-SHTF.
On a personal level, decoys may be used to misdirect hostile intentions from yourself, luggage or personal valuables. Proper usage may convince an aggressor that he has what he set out to get in the first place or convince him there is nothing to be had.
On a larger scale, decoys can act as “sacrificial” elements to deter loss of critical provision and equipment from theft or burglary and may take the form of smaller caches, stockpiles, dwellings or vehicles.
Decoy usage on a larger scale will largely depend on personal resources and time to carry off a convincing ruse, whereas personal scale decoys are mostly a matter of pre-planning and quick action.
A couple of examples are presented below that you can easily employ to improve your personal preparedness if you choose, and are even more effective as part of a holistic plan.
Decoys are not appropriate or feasible for every situation. I have included commentary and a few key questions with each to help you critically evaluate your own ideas before implementation.
Decoy Wallet
A time-honored, classic anti-mugging decoy and one that takes only a little material and ingenuity to implement.
The idea is you carry a separate “fake” wallet, money clip or whatever alongside your actual one. Inside this decoy wallet, you will have numerous small denomination real bills, or convincing fake ones (use prop money, don’t print your own!), and either never-activated promotional cards or old gift cards that lend the same appearance.
You may utilize a fake ID card of some type but this is not strictly necessary. Whatever is in the wallet should in no way indicate your address or identity!
In execution, if you are ever held up you can assume your assailant will demand your wallet. Producing the decoy wallet, you can “accidentally” drop the wad of bills and/or throw the wallet down at their feet and utilize the distraction to beat feet out of the situation. Most robbers will be content to plunder their ill-gotten gains in lieu of pursuing a fleeing mark at that point.
The joke will be on them when they turn up perhaps $20 and a slew of empty gift cards. If you are cornered when the mugging occurs you can use this distraction as an opportunity to counterattack.
Hidden in Plain Sight
Lots of people keep supplies and other equipment in their vehicles and often do so in their bug-out bag or other piece of luggage.
It is understandable and often advantageous to keep survival equipment in your vehicle, but the obvious problem with that strategy is the risk of theft, especially if your gear is visible in the cabin. It is less likely to invite theft if kept in the trunk, but this of course does nothing to prevent theft if the car is broken into.
Nonetheless, the appeal of keeping a stash of gear with you wherever you go is strong, and some may want to keep their items accessible at a moment’s notice by keeping them in the passenger compartment.
The solution once again is a decoy of sorts. You will only need a couple of things to carry off this ruse: a 5-gallon utility bucket with a lid, an old paint roller, tray and handle, and a small quantity of latex paint. Should you already have these items lying around and gribbly looking, so much the better, just clean the inside of the bucket well.
If you are starting with a clean bucket, start by sealing your bucket with the lid and then roughing up the exterior so it does not look new and shiny. A general patina of dirt and grime will help sell the deception. Then further season your bucket with some splashes, spatters, and dribbles of paint.
Do the same to the paint roller. Let the paint on both dry, then wrap the roller in a plastic grocery bag, trash bag or roller cover. That takes care of our decoy.
Now simply load your packed bag into the bucket (if it will fit) or place your emergency items inside separately. Now you can set your kit with “dressing” consisting of the used roller, tray, and all into the floorboard or backseat of your vehicle free from concern that it will attract any unwanted attention from thieves.
Does a pile of painting tools inside a DIY-ers car make a tempting target? Who steals used paint supplies? Compare that to the fact that any exposed pack or bag may make a tantalizing enough target for a motivated thief to break in and you can see the obvious value here.
In a pinch, you can pop the top, don your pack and take off. Your supplies have stayed clean inside your unused bucket.
Decoys around the Home
Decoys in the home have many uses. From the false safes mentioned above to lightly equipped stashes of valuables, gear, and other items, decoys of this nature can convince would-be thieves and intruders that they have scored when they have in fact gained nothing.
When considering the former category, think as a burglar might. Even novice burglars will ransack likely hiding places for valuables of all kinds: guns, cash, jewelry, electronics, gold, and so forth.
If they expect to find something and do, they may be content to high-tail it out of your home with what they have, especially if an alarm system is blaring or they are already under pressure.
A jewelry box stuffed with convincing but ultimately worthless false gold or gemstone jewelry will seem like quite the prize under the circumstances.
Especially if our intruder had to dig a little bit for it that may spell the end of their burglary. Similarly, a strong box hidden amongst the other items in your closet and filled with stacks of fake bills and useless coinage will serve the same.
Guns too can be protected in a similar fashion. Acquire a few intact but very cheap or broken junker guns, and take the time to have them rendered inoperable. There are a few things you could do easily depending on the make and model of the gun; welding up the chamber, bore or breechface, removing the firing pins and perhaps filling their channels and so forth.
Set these decoy guns in obvious places of storage like dresser drawers, behind closed doors, over mantles, and prominently displayed over fireplaces.
These decoy firearms will be greedily grabbed by our burglars and hopefully they will abscond with those and nothing more. At any rate, you can sleep soundly knowing that no one will be harmed by the deactivated guns taken from your home.
Note that all of the above examples will only stand a chance of working as intended if the actual targets, your valuables, guns, and provisions, remain well hidden. A false gun next to a real one only means your burglar gets one working and one fake gun.
Decoys on Defense
If you start thinking bigger picture, decoy tactics have nearly limitless applications and are highly effective. Some larger-scale employment could require considerable time and resource investments but may very well make all the difference in a long-term crisis.
If your bug-out location can make use of a hidden, secondary shelter, either within a dwelling or not, you can make use of your primary shelter as a decoy itself.
Keeping your hidden shelter well-stocked with equipment and provision (space allowing) and leaving your primary shelter in carefully “picked-over” disarray can readily lend the impression to any looters or uninvited guests that they have wasted their time and a trip.
You can do something similar with a property you own by keeping an old cabin or trailer there while depending on a carefully camouflaged and hidden secondary dwelling or even an RV.
Take care with both of the above methods that you leave no sign, trace or track to your hiding place that may be detected by intruders.
The same principles can be applied to hidden prepper caches located in urban or rural areas. Believe it or not they can get discovered by deliberate action or by accident, even when well-hidden, and having a decoy in place may mean the difference between a lost cache and ready resupply.
If burying a cache in soil or sand, a classic trick of leaving a decoy container directly above your actual stash container will fool the lucky finder or determined searcher. If your decoy contains a few things that will sell the subterfuge, even better. An alternate method is to bury or hide one in an obvious location earlier on your path to your actual cache site.
A more esoteric but viable decoy on defense is that of a false target: if you are expecting trouble, you can set up a mannequin or similar human form in an area that an attacker will encounter unexpectedly.
If sufficiently convincing (say, armed with a “gun” and remote or motion-activated light) this decoy may draw your attackers into revealing themselves or moving into an unfavorable position.
Auditory Decoys
Remote or motion-activated noisemakers of all kinds have merits in a comprehensive defense plan. A high-quality recording of a voice or noise like a dog barking may serve to distract intruders or lead unwanted attention away from your location.
A teammate or family member working in tandem with you to confuse or distract opposition works just as well. Compared to more tangible decoy methods, auditory decoys require more finesse to use well and get results, but they work well to add fidelity to already comprehensive deceptive tactics.
Around the home, recordings of activity in the home, played when you are not there, in conjunction with lights and other signs of occupancy may sell the illusion that the home is occupied.
On defense, a vicious dog barking is often signal enough for would-be invaders to peddle their trade elsewhere. Any sound of furtive movement like doors opening or closing, footsteps and one-sided conversation also conveys an active occupant.
Decoy Failure
Decoys will often fail from not being convincing enough, either from a lack of fidelity, poor location, or both. In the examples above I mentioned a false strongbox that was too light; obviously, it is empty. An empty strongbox has no value to a potential thief.
Once the thief picks up the empty decoy strongbox, they know it is worthless. They may not know it is a decoy, but they know they should keep looking in your house for loot! This is a classic failure of low fidelity.
Consider a decoy gun placed among your real guns. Not much point, as mentioned above: the real, valuable working guns will be stolen right alongside your decoy!
This would be an instance of location failure. Alternately if you used a decoy gun that was obviously broken, incomplete or fake, that would make for a low-fidelity failure.
An auditory decoy with the speaker or source placed outside, within line of sight of your adversary, would be a potential location failure: a dog barking or similar spoof would be found out to be obviously fake.
Decoys can also fail to work if your foe is very crafty. A clever one may see through your ruse, or have been tricked before.
Even in the animal kingdom, a decoy encountered multiple times or subjected to prolonged scrutiny will lose fidelity if supplementary measures are not undertaken.
Consider the case of our scarecrow way back at the beginning of this article: how many times have you seen birds, including crows, perched on one? A bunch, right? Right, because the decoy has lost fidelity. A scarecrow is supposed to represent a man, our farmer, who birds avoid as he works in the fields.
If the scarecrow is not moved, repositioned, etc. it loses fidelity because the crafty crows begin to understand it is no man at all, and thusly no threat. Soon they are going about their business without a care in the world.
Our human adversaries may be like our crows above. They may be so thorough that they do not stop without verifying all possible hiding places, patting you down, or some other countermeasure against your deception.
They may employ a tactic that simply busts your plan, or approach in such a way you’re your decoy is ineffective, leaving you moving for a Plan B solution.
Decoy Planning Process
The following six-step process will help you analyze your situation and create a decoy that may work against potential threats.
Used judicious reasoning: decoys can be made to work in almost any situation but are rarely a one-size-fits-all defense. Again, they work best as part of a comprehensive defensive plan, and as always you should be able to kick ass if you need to should escape or evasion fail.
Step 1: Determine the Threat – What/who is the threat? Where are they likely to approach from? What is the threat likely to key on?
Step 2: Determine Target- What does the threat want? What does the threat consider a lucrative use of effort?
Step 3: Determine Goal- “Spoof home invaders/burglars with fake loot” or “distract mugger with valuables to enable escape/counterattack” etc.
Step 4: Assess Decoy Requirements – How much realism does decoy need to function? How about placement requirements? Under what conditions and time constraints will the threat be encountering decoy? How will that affect decoy design?
Step 5: Select/Design Decoy- Purchase or create appropriate decoy and test for function.
Step 6: Evaluate Plan- Does the decoy pass muster as a realistic target under the circumstances? Is the decoy compatible with my day-to-day plans and procedures? Does the decoy require user activation/operation, or is it autonomous or inert? Does it require maintenance and upkeep to maintain operability or effectiveness?
Other Considerations
Consider this article an entry-level guide to decoy usage. The above info deals with decoy usage against a human adversary or adversaries unaided by any technological tools and gadgetry.
Against a bad guy or hostile force equipped with things like telescopic aids, night or thermal vision sensors, aerial surveillance, and so forth, decoys must take on a corresponding level of sophistication to remain viable.
Hopefully, you will not find yourself facing such well-equipped enemies, but the situation is far from impossible and getting more likely all the time. Consider how the now common drones have changed the landscape of observation and scouting, even in the civilian world.
If you were trying to remain hidden how might one of these quiet eyes in the sky affect your plans? What could you do differently to conceal your location, or feed it the wrong picture?
Decoys that fool one sensory method (the eye or other visual sensor for instance) may not work at all against another sensor. Thermal sensors will not be fooled by a mannequin that is ambient temperature. Metal detectors are not fooled by a covering of earth or many other materials.
If you must confront an electromagnetic sensor with a decoy, the decoy must be attuned to the sensor or it will be useless. Threats that rely on multiple spectrums of sensors will be significantly harder to fool with decoys.
Conclusion
Decoys are rare tools that allow a defender to attack his opponent’s thought process directly by hijacking his perceptions. Used with care and skill in a quickly-emerging scenario, the resulting blunders and wasted time provide ample opportunity to fight back or escape danger.
In long-term situations, a decoy may convince your would-be attackers to look elsewhere for what they desire. By taking the time and expending the effort to understand and incorporate decoys and other deceptive elements into your preparedness plan you will be better equipped to give the bad guys the slip.

Charles Yor is an advocate of low-profile preparation, readiness as a virtue and avoiding trouble before it starts. He has enjoyed a long career in personal security implementation throughout the lower 48 of the United States.

Excellent article! Good information, well presented. I do have a few thoughts that might be of interest:
1) Sacrificial items were mentioned, but not much detail given. I believe that they can play a significant role in the successful use of decoys. One reason is that the item(s) are real, with actual usefulness or of value to the person taking them. Nothing needs to be faked.
If you use an item you have in abundance, especially a low cost but highly desirable one (chocolate, 50ml bottle of liquor, a (very) worn silver dime in with something else, etc.) the person is more likely to stop looking and move on out of fear that they are going to get caught, and since they do have something ‘good’ they will not want to risk losing it.
You do not want things set up so the person will be encouraged to keep looking with the hope of finding more. It needs to look as if it was left behind by accident, or the place was already searched and the item missed by another looter.
2) A sacrificial item can be one that is real but has an addition included that can be either a tracking device or something that will incapacitate the person taking it within a short time frame. Long enough to not raise too much suspicion, or give the person or those with him/her incentive to go back and extract vengeance, in the case of the person being incapacitated. If it is a tracking device, it should be with something that will not be used and discarded soon after having been acquired.
3) Something with very tempting information might be left behind either not concealed well, looking like it was dropped by accident, or it can be something that is coded, but with the decoding information somewhere it will also be found, but not too obviously. Something such as a child might have written down so they would not forget where the ‘hidden cache of food (water, weapons, ammunition, or retreat) is located’. Could be something close that lends itself to setting up a hasty ambush, or something quite some distance away so the likelihood of the person/people coming back is low.
4) Similar to that just above, an item or information that will lead the person(s) straight into an ambush or situation where he/she/they can be easily dealt with in some other way.
5) An item or multiple items that will likely keep the person/people on location for a longer period of time to either give time for a person to escape or time to get to a cache or support group to get what is needed to take on the looter(s), or where one find leads to another that winds up pulling the person/people into a situation from which they cannot escape.
6) Another type of decoy can be something that looks innocuous, so anyone approaching it will not think of it as a danger. But since booby-traps are illegal, it would be a device that can be used to stop a person or group to be incapacitated in a non-deadly manner once he/she/they are all within range.
7) Some people simply cannot resist figuring out something that is not immediately obvious. If you suspect someone specific is likely to try and steal something from you if a disaster occurs, and the person(s) is that type, a decoy that will keep the person(s) interest for a while trying to decide what it is, how to get into/around it, or some other aspect that will hold that person’s interest long enough for you to do whatever it is you have decided ahead of time to do if the opportunity presented itself.
8) If a person is generally known as a prepper, or even if just strongly suspected to be one, chances are people will show up looking for (at the very least) a handout. Or will simply come to get what they know/think you have simply because they do not have any of their own. Simply having everything well hidden will not be enough to convince that type of person that there is nothing there. The mindset of such people is usually that they are smarter than the average bear, and are right about you having something, and are just a bit better at hiding it than that person thought you would be. So they will keep searching. And likely be doing some hurting to either you or someone you care about to make you talk. (And if you do not actually have anything, it will get really bad really fast. Why you would be in that position I cannot imagine, but I guess some people might be.)
This is where decoys can be an absolute necessity. It is better for someone like that to find and take a decent amount of goods than to hang around and keep looking if they believe you have more. So the sacrificial find has to be enticing enough, to them, for them to be satisfied and walk away without having done too much damage to you, your family, or your place.
Depending on what they might actually know about you, providing that thing or those things in fairly small quantities the loss of which will not endanger you, and something to make them to really believe you never actually had more, or if you did, it is now gone, you have a good chance of getting yourself and your family out alive, with the bulk of your supplies intact.
You can either very convincingly stall a bit and finally (way before the pain starts) admit that you are simply a braggart and did not really store up very much, with the right acting, the person/people might believe you. Especially if they already do not think much of you for your politics, favorite football team, or some such. People really think they are smarter than you, especially when it comes to outsmarting someone. Of course, they can do it, but no one can do it to them since they are too smart. They all seem to believe that way.
Or, if you are a pretty good actor and especially if you are known to be an easy touch or have some greedy kinfolk, and things ramped up a bit slowly, you might be able to convince those that have come for your stuff that ‘Sure, I had some stuff. But my onery “insert family member or other deadbeat here” came crying to me and I had to give him/her/them what I had because of his/her/their situation and now they are long gone and I am stuck with nothing, since when I had my back turned to help load one of them sneaked out with the stuff I was saving for myself.
Might or might not work, depending on the whos involved and your acting ability.
9) Bluffing with a decoy. I would be very careful with this one. Desperate people will often call a bluff. Simply because they are desperate enough to want something badly enough they simply cannot believe that you would be able to do what you are saying since they need/want whatever it is they need/want so badly their mind blocks out the possibility. Once a bluff is called and it turns out it was a bluff and not what you said, then they will never believe you again, so you will not be able to bluff them in the future most likely, giving up a powerful tool that could be important. Bluffing is a very last chance risk to be taken.
Thinking outside the box can help with coming up with decoys, but it can also be a risk. Because it has to be thought through from several mental vantage points. What seems obvious to you might not be to someone else. And just the opposite can be true, as well. Something that never occurs to you, due to your experiences, may be very obvious to the other person, because of their experiences.
There are lots and lots of ways to use decoys. Have what you need to create several different kinds, for different reasons ahead of time. You probably want to have some of them already made up.
Just my opinion.
Then there is the “anti-decoy” concept. You mention non-working guns which look valuable. How about a valuable gun (or other item) which is made to look “useless” or at least “undesirable”?